How to evaluate the impact of LLMs on business outcomes
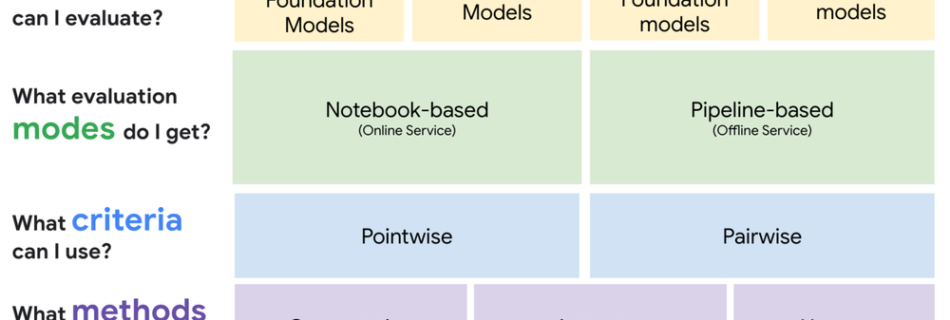
How can you make sure that you are getting the desired results from your large language models (LLMs)? How to pick the model that works best for your use case? Evaluating the output of an LLM is one of the most difficult challenges in working with Generative AI. While these models excel across a wide …
Read more “How to evaluate the impact of LLMs on business outcomes”